The security level of high-security locks and distributed systems is to increase with the new version of VdS standard 3841 and the subsequent update of EN 1300. But are these requirements sufficient? And what happens with existing installations?
Cash handling and transport are subject to economic constraints: processes have to be organised in an efficient and cost-saving manner, but without compromising safety. Electronic locks, often even networked, have established themselves as a solution for ATMs, safes and lockers. For this reason, in addition to the protection classes for high-security locks, there are other directives and standards that focus in particular on electronics and IT networks in order to ensure a high level of security. The EN 1300 standard, for example, should be mentioned here.
But the VdS property insurance association has also taken up the subject and has drawn up its own guideline. “VdS standard 3841 covers the requirements for locks and locking systems as well as wired or wireless transmission systems,” explains Head of Sales Detlef Lücke from INSYS locks, who is participating in the WG3 working group on the new EN 1300 standard.
The threat situation has changed
In view of technological developments and changing threat scenarios, it is essential for these standards to be regularly adapted in order to maintain a high level of security. For example, in its draft of VdS 3841, among other things the VdS refers to the short innovation cycles of electronic applications, but especially in the IT sector. Accordingly, test methods could be adapted to current developments at short notice if necessary.
At the same time, the VdS is aware that networked systems can be complex and multifunctional. The guideline therefore also refers to other requirements that may be affected, including the VdS guidelines for fire protection and security technology as well as for burglar and alarm systems.
Technology already adapted to future standards
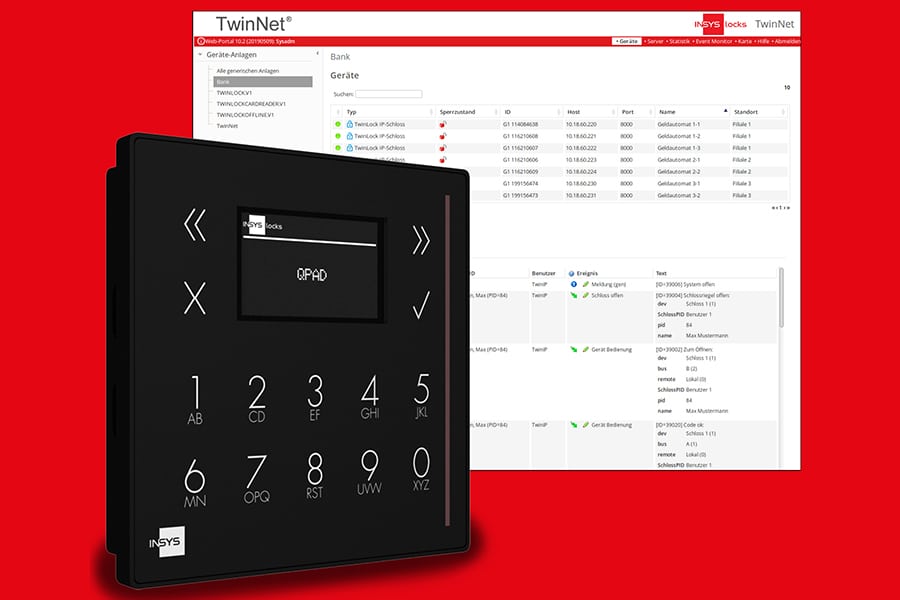
As part of the amendment, the VdS is introducing a new certification level for networked locking systems. In addition to the previous categories 1/2/3/4, categories 1+/2+/3+/4+ will be introduced for networked systems. The current versions of the TwinLock® product series of INSYS locks are to be tested and certified according to this new level.
“Our goal is 2+/3+/4+ classification,” says Head of Development Mario Bauer. The certification process is underway and should be completed by the middle of the year. In order to obtain these certifications, the manufacturer has revised the lock software to implement new functionalities and higher security standards.
One change concerns the update process: with the requirement to keep systems up to date with the latest technology, it is now essential that a lock can be equipped with new firmware, Bauer emphasises. In addition, it must be ensured that this process is really secure and does not itself open up a risk of attack.
Keeping an eye on operational safety
Among other things, the VdS guideline stipulates that in the event of a power supply failure, historical data such as logging of accesses or firmware updates must be stored securely. In spite of this, a failure of the network connection – whether due to a power outage or problems in the network or with a central server – carries risks. Under certain circumstances, the lock may no longer be able to communicate with other locks or a central database.
In such a case, the mechanism of the network locks of INSYS locks switches to an autonomous offline mode. Since the access codes are stored in the lock and don’t have to be obtained or compared via the network, the locks can still be opened and closed with the existing codes and are not impaired in their function.
“Although high network availability is guaranteed today, 99.99 percent availability still means a total downtime of 52 minutes per year,” explains Detlef Lücke. “And if the door to the customer’s safe fails to open or the vault doesn’t close at the crucial moment, then the bank has a problem”.
In offline operation, accesses are logged in an internal memory in accordance with the guidelines, and are automatically transferred to the central server as soon as the network connection is available again.
Exemption of existing systems versus complexity
The new standards do not initially apply to existing equipment, which is exempt. However, if new locks are later added which already comply with the new directive, things could become complicated because then devices with different functionalities are installed in the same network.
Such mixed operation is technically possible without problems, but in practice a uniform platform is much more efficient for IT administration and handling. Lücke calls this “convenience”, and is referring to the combination of high security standards with ease of use for customers and users. This is not just about convenience, but about cost and time benefits resulting from clear and quick usability.
Since the necessary changes are purely software-based, installed systems can simply be adapted to the new security requirements via updates. INSYS locks has therefore decided to offer this update option to existing customers. Depending on the customer’s requirements, all locks can be upgraded with a complete or step-by-step conversion to a uniform range of functions and at the same time to the current, higher security level. Future changes can also be imported retrospectively.
EN 1300 is being updated
Just like the VdS, the “Safe locks working group”, which is preparing an update of the currently valid EN 1300, refers to ever new break-in methods. The most recent update was increasingly dedicated to attacks on electronic controls by various means, including attacks using electromagnetic rays or the targeted application of electrical voltages. As a result, new immersion, EMC and shock tests have been defined. In addition, the requirements for the firmware of electronic locks have become more stringent.
In future, attacks via the network will increasingly be taken into account. A corresponding assessment of the security of distributed systems is in preparation. This includes, for example, the requirement to use the latest cryptographic methods when generating keys and pairing components in the network. This new version will probably be published in the year after next as EN 1300:2021. Here too, INSYS locks has already reacted and included the relevant encryption algorithms.
Investment in customer security
INSYS locks has its own TwinNet® management software, which works together with the TwinLock® locking systems, regularly tested by recognised German testing institutes for IT security. Penetration tests are used to determine whether the software is vulnerable to attack. Any weak points found are consequently eliminated immediately.
Further proof of the security of the management software is provided, among other things, by clearance certificates from Fiducia-IT and GAD, the IT service provider at the Volks- and Raiffeisen banks, as well as the OPDV (correctness and auditability of data processing) approval of the Sparkassen-Finanzgruppe. “These tests and certifications meant considerable investments for us, but are indispensable in view of today’s cyber attacks,” emphasizes Detlef Lücke.
“The functionality of a solution, i.e. the locks, network and software application, is a significant argument in the decision-making process. In addition to the locks and the TwinNet® management software, the IT security of the overall system plays a decisive role,” adds Mario Bauer.
This article was originally published in German in IT-Banker – Issue 01, 2020 (publication date: 26.02.2020):
